Other - Management and Security
Introduction
In order to properly manage the entire project in a team, data security has to be considered and management tools have to be in place.
This section has four parts: active directory, user accounts, access control, and logging.
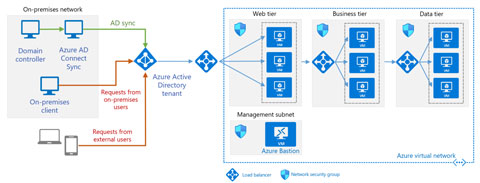
Active Directory
In order to provide centralized management, Microsoft's Active Directory was adopted. Each user has its own account with different permissions on different machines.
In addition, AD would greatly benefit us on Windows server deployment. The configurations can be set using GPO and applied to all machines together. Deploying Active Directory is a separate project, and for more information, please refers to AD Project.
User Accounts
In general, each user will have their own account. Each user will have access to a private data directory and a public shared directory. These directories are hosted on one of the storage nodes in AD and were mounted using GPO. Whichever computer that the user logged in, those directories will be mounted automatically.
For matters like downloading where several users need access to the same screen, a dedicated account will be created. These kinds of account was tied to a specific service and will be disabled upon project completion.
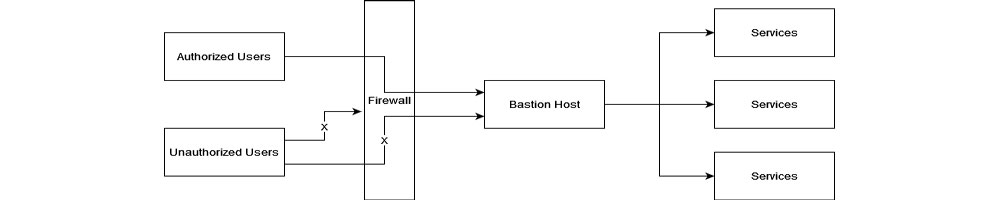
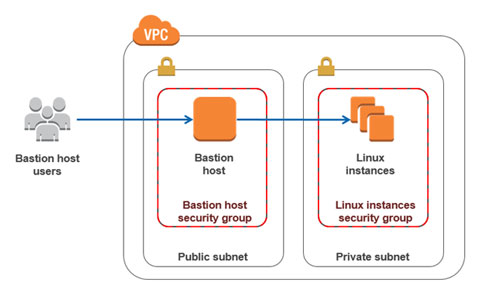
Access Control
It is a bad practice to expose ports of all services to the public internet, especially since most of the services are not public services. A proxy server or bastion host was then created. Except for web services that hidden behind the reverse proxy, only the bastion host was exposed to the internet. The user has to log in to the bastion host before it can access LAN services and servers. This can greatly reduce the possibility of being hacked.
In addition, not all user has access to all the server, even if they are all project members. All the users have access to the bastion host, but permission to log in to the production servers is granted on a per-user basis.
Logging
For most of operations or all operations of data downloading, a log will be generated and stored in the database automatically. This makes all operations traceable.