Internal Proxies Project
Project Concluded: August 22, 2022
DB Reference: dc_access_internal_proxies
Last Updated: September 26, 2023
Introduction
Security is a critical aspect of any data center or server cluster. As a novice in network security, I did not have sufficient knowledge and time to conduct in-depth defenses. Therefore, instead of exposing all management interfaces to the public web, I decided to restrict them to the LAN, which can be accessed via a group of VPNs or proxies.
This project aims to provide a set of secure access protocols to safely access the datacenter remotely.
Specification & Structures
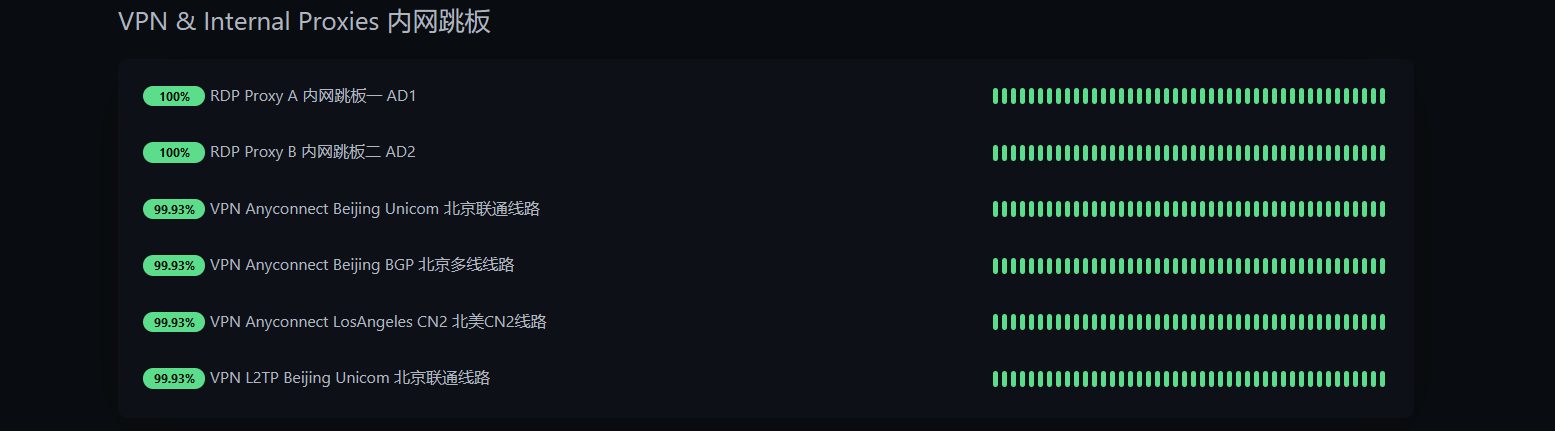
As of April 2023, the system has the following specification:
Hardware: 3 * Windows Server 2019 VM each with 4 Core and 12G memory
VPN: 1 * AnyConnect Server
VPN:: 1 * L2TP Server
Access Point(s): All(HK01;BJ01,02,03;LA 01;LV 01)
Detailed Description
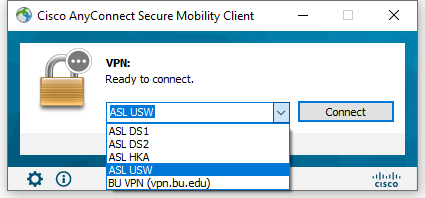
The current VPN setup comprises a Cisco AnyConnect server (via Ocserv) and a standard L2TP server. For most purposes, AnyConnect is used due to its flexibility. However, in situations where obtaining the AnyConnect client is not practical, the standard L2TP can be very helpful since it is a built-in function of most modern devices.
The current set of proxies consists of three Windows VMs running Windows Server 2019. These proxies were deployed on two hypervisors across two existing Active Directories to ensure that our administrators can access the internal LAN during a hypervisor or AD failure. Each proxy is closely guarded by software firewalls and security software. Additionally, the RDP port of each proxy is mapped to all network access points, allowing operators to always access the data center via the best network route.
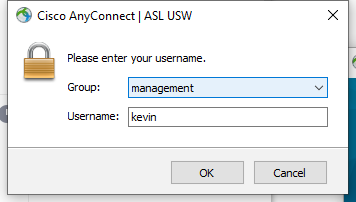
L2TP is a global layer-2 VPN, while AnyConnect operates on layer 3. To facilitate access and avoid redirecting all traffic, I configured the server to use split DNS and group-based policies. Each group has a different routing policy for different purposes, and each user has different permissions for the groups they are allowed to connect to.