Datacenter Security
Introduction
Security is ubiquitous, from physical systems to software. It is vital to ensure the security of the datacenter in order to safeguard the hosted data from all angles. As I am not a security professional, I can only do my best to implement security measures.
This part has been divided into two categories: physical-level protection and software-level protection. In the interest of security, information on this page has been limited. If you encounter any inconsistencies or unexpected decisions, it may be due to undisclosed factors related to security concerns.

Goal
The objective is to implement security measures for the datacenter at both the physical and software levels. In the event of a breach, the impact should be limited in scope, and the potential for data leakage or damage should be minimized.
Physical Security
Walls
Fortunately, the walls of the datacenter building are thick enough (about 0.5m) to greatly reduce the likelihood of a breach.
Windows
With the walls being secure enough, my attention turns to the windows. It's clear that I want the windows to be as strong as possible. Additionally, if the windows are designed to be opened, then the opening mechanism becomes a potential weakness. Since we have a full ventilation system, I believe it's safe to seal the windows. As a result, we have installed two pieces bulletproof glasses. Although it's unlikely for someone to shoot at the windows in China, bulletproof glass provides enough strength to delay an intruder until the police arrive.

Access Control
Since there will be multiple operators, particularly when I'm not present, traditional key-lock pairs are not appropriate. Consequently, an enterprise access control system was deployed.
It can be dangerous if someone is inside the datacenter during a power outage. In such a scenario, the ventilation system and access control system will stop functioning. Since the windows cannot be opened, it poses a potential danger of suffocation to anyone inside. To address this issue, I have opted for a lock module that automatically unlocks when the power disconnects.

Power Distribution Cabinet
To prevent intruders from gaining access to the datacenter by cutting the power, a power distribution cabinet was installed inside the datacenter. It's impossible to cut the power from outside unless you know where to dig.
Surveillance
A surveillance system has been installed both inside the datacenter and on the exterior of the building. A combination of 180-degree and 120-degree cameras have been utilized to ensure there are no blind spots. Additionally, all cameras feature night vision and smart detection. The video footage is stored on high-capacity disk arrays, which can store months of historical data.
Network Security
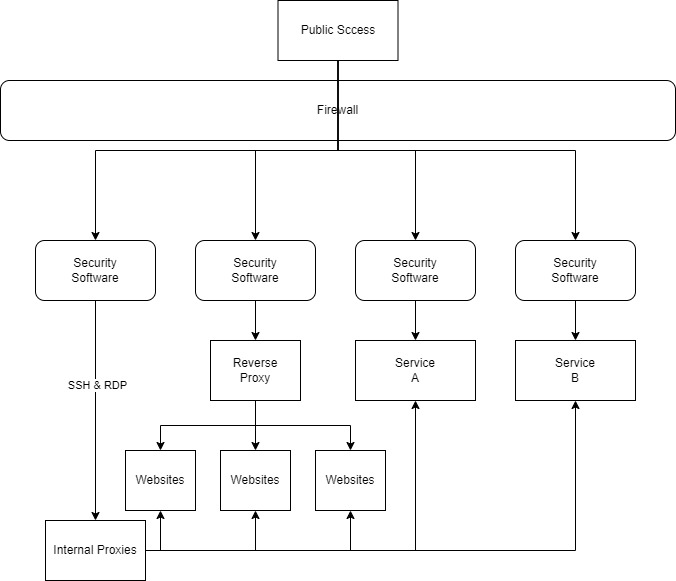
VLAN
As I am not a professional in network security, I began by limiting the scope of potential impacts. To achieve this, I configured different VLANs for different servers and virtual machines. For remote access administration, a set of proxy servers were used. For more information about VPNs, please take a look at Internal Proxies & VPN Project.
Isolation
Since there is a mix of Linux and Windows virtual machines, I opted for VMware ESXi as the hypervisor. Unlike Kubernetes, ESXi is a complete hypervisor that provides full isolation between virtual machines. Each application will generally have its own VM to provide a better isolation and reduce the impact scope in case of a security breach.
Software
To deploy services, only official sources were utilized. I refrained from using third-party scripts unless I was certain of their contents.
Port Limitation
All web services will be shielded by a reverse proxy. For other types of services, only the service port was exposed. Control protocols, such as RDP or SSH, are only accessible via certain VLAN and proxy that are guarded by a mature firewall and safety software. For more information about proxies and optimized routes, refers to Global Access Points Project.
The Future Work
Improving physical security doesn't seem to be feasible, and enhancing network security is beyond my current skillset and available time. However, two major plans are currently underway to improve security.
- The first is to add an uninterruptible power supply (UPS) to the access control system to ensure security even in the event of a power failure.
- The second is to utilize a Trusted Platform Module (TPM) module and full disk encryption to safeguard all the data.
These plans, however, require further study on their potential impact on performance.